Dark Web Directory (2026): Verified Onion Sites List, Categories, Safe Access Guide & Updated Links
Last Updated: May 2026 | Editorial Review: Verified for Accuracy
The vast majority of the internet remains invisible to standard search engines like Google and Bing. In fact, the surface web—the part of the internet you access every day—makes up only about 4% to 5% of the total internet. The remaining 95% is made up of the deep web and the dark web, massive layers of data that standard search crawlers simply cannot reach.
You might feel overwhelmed when trying to navigate the hidden corners of the web, but you are not alone in your curiosity. Accessing these layers is often difficult because onion links change frequently, and many directories contain broken or dangerous paths. The landscape is constantly shifting, requiring users to stay updated on the latest access methods and security protocols.
In this comprehensive guide, you will learn how to find active directories, verify onion links, and protect your identity while browsing. We will look at updated categories for the current era, provide a curated list of safe .onion site examples, and offer a clear path for beginners to follow. Whether you are a journalist looking for secure communication channels, a privacy advocate, or simply a curious tech enthusiast, understanding the mechanics of this hidden network is essential for safe exploration. To further enhance your privacy journey, we recommend reading our guide on how to stay anonymous online in 2026.
⚡ QUICK ANSWER
To access the verified onion sites list for 2026 safely, use the latest Tor Browser 15.0.13 and a reliable VPN to hide your entry point. The main cause of failed access is using outdated ".onion" URLs that are no longer active. Always verify links through trusted community aggregators or a verified dark web search engine. The fundamental rule for the current protocol is layering your security: start with a premium, no-logs VPN, route your traffic through the Tor network (updated to Tor 0.4.9.8), and never deviate from the default security settings of the Tor Browser.
Live Technical Specs (Verified May 2026)
- Current Tor Browser Release: v15.0+
- Core Tor Version: 0.4.9+
- Supported Address Type: V3 Only (56 characters)
- Link Integrity Check: May 11, 2026
What is a Dark Web Directory?
A Dark Web Directory is essentially a curated list of websites that end in the ".onion" suffix. Compared to the regular web, these sites are not indexed by traditional bots—users rely on these directories to find content. It serves as a map for the encrypted part of the internet. Think of it as the "Yellow Pages" of the darknet. Because there is no central domain registry (like ICANN for the surface web), finding a new site without a directory is nearly impossible unless someone directly gives you the link.
People use these lists because finding specific services requires knowing the exact, scrambled address of a site—these directories organize links into categories like forums, email providers, and research archives. Using a directory is the most common way to discover new pages without getting lost. Many users start with the Hidden Wiki 2026, a well-known example of such a directory, though one must always verify its current address to avoid phishing clones.
The Evolution of Onion Directories
Over the years, these directories have evolved from simple, static text files pasted on forums to highly structured, community-moderated platforms. Below is a comparison of how directories have changed over the years leading into the current era:
| Era / Year | Directory Format | Security Features | Link Verification Method |
|---|---|---|---|
| 2010-2015 | Static Wikis (e.g., The Hidden Wiki) | None (Plain HTTP) | Unverified, user-submitted |
| 2016-2020 | Dynamic PHP Sites | Basic HTTPS, Captchas | Manual admin review |
| 2021-2024 | V3 Only Platforms | PGP-signed links, Tor metrics | Community upvotes/downvotes |
| 2025-2026 | AI-Assisted Aggregators | Automated phishing detection | Cross-referenced with multiple dark web search engines |
Why Do Onion Links Look Like Random Gibberish?
If you are new to Tor, you might wonder why addresses look like xmh57jrzrnw6insl.... It isn't random; it is cryptographic math designed to replace the need for a central registry.
Think of an onion address as a digital fingerprint derived from the server's unique "public key." Because the address is mathematically generated from that key, your Tor browser can mathematically prove that you are connecting to the legitimate server holding the matching "private key."
This means no central authority can forge the address, and there is no "Domain Registrar" that can be hacked or subpoenaed to reveal the owner's identity. In the current V3 format, these addresses are 56 characters long, providing a massive level of security against typosquatting and impersonation. If you are interested in the specifics of how these keys protect your data, our what is PGP encryption guide breaks down the technology in detail.
Types of Dark Web Directories in 2026
Not all directories are created equal. Understanding the differences between them is crucial for your safety:
- General Directories: Broad lists covering everything from email providers to marketplaces.
- Niche Directories: Focused on specific topics like whistleblowing, academic research, or privacy tools.
- Automated Aggregators: Scripts that constantly crawl the Tor network for new .onion addresses and automatically list them. Note: These carry a higher risk of indexing phishing sites.
- Hardcoded/Trusted Lists: Directories maintained by well-known privacy advocates or organizations, often signed with PGP keys to prove authenticity.
Verified Communities & Forums
One of the most significant changes in the current era is the reliance on community-driven platforms for verification. Forums are no longer just for discussion; they serve as live directories where users report scam sites instantly.
The Status of Dread
For many, the Dread forum remains the "holy grail" of dark web information. Dread serves as a Reddit-like platform where users discuss marketplaces, vendors, and security. Because it is a forum, finding the current address can be tricky as it changes frequently to avoid DDoS attacks.
When looking for the working link, never rely on a Google search. Instead, use cross-referenced links from trusted clearnet sources that mirror the forum URL. The current working link is essential for checking the reputation of other sites before you visit them.
Other Notable Forums
Beyond Dread, there are specialized communities. For those interested in hardware and cybersecurity, darknet forums often include sites like DarkForums. Finding the correct link or verifying the status usually requires an invitation or a referral from a trusted user on Dread.
Safe & Verified Onion Sites Examples (2026)
For users looking for safe .onion sites to test their connection, sticking to major, legitimate organizations is the best practice. These sites offer compliant resources without the legal risks associated with darknet markets.
Official Corporate & Archival Mirrors
Many mainstream organizations maintain onions to protect user privacy.
- The Tor Project: You can always find the official Tor Project onion address to ensure you are downloading the correct software or reading news without censorship.
- Social Media: Surprisingly to some, Facebook has had a presence on Tor for years. Users searching for the current Facebook onion address can access the platform to bypass restrictive firewalls in certain countries.
- Archives: For researchers, the Internet Archive onion address and the Archive.is onion link are indispensable. These allow you to view snapshots of websites that may have been deleted or censored on the clearnet.
- Whistleblowing: Those seeking leaked documents often look for the current Wikileaks onion address. While links shift, the Wikileaks onion remains a staple for investigative journalism.
Niche & Specialized Directories
Beyond the general hubs, specific communities have formed around specialized tools and content.
- Search & Libraries: Finding specific files requires knowing where to look. The Tordex onion address is a popular search engine within the network, acting similarly to Google but for .onion sites. Additionally, for Russian-speaking users or those looking for specific digital assets, the Rutracker onion link provides access to a massive torrent repository.
- AI & Tools: Emerging technologies have found a home here as well. Users experimenting with unfiltered AI models often search for the OnionGPT dark web onion link. These tools are experimental and should be used with caution.
- Niche Link Lists: Smaller, curated lists exist for specific subcultures. For example, the Cebulka onion link is often cited in Eastern European circles for specific resources, while those searching for utilities might stumble upon the Cracking Island onion link. Warning: The latter is a high-risk area and requires strict skepticism.
Bento Grid Layout: Directory Categories (Active)
Active directories in the current era organize content into visual tiles. Below is a simulated Bento Grid of the landscape, categorized by risk and utility.
text
+---------------------------------------------------------------+
| 📡 COMMUNICATION & PRIVACY (Low Risk) |
| |
| • ProtonMail .onion • SecMail • Tor Project Mirrors |
| • Signal Foundation • Riseup • Ello |
+---------------------------------------------------------------+
| 📚 RESEARCH & ARCHIVES (Low Risk) |
| |
| • Internet Archive • Sci-Hub • WikiLeaks Mirror |
| • Archive.Today • Global Leaks |
+---------------------------------------------------------------+
| 🛠️ TOOLS & UTILITIES (Medium Risk) |
| |
| • Tordex Search Engine • OnionGPT AI (Experimental) |
| • SecureDrop (Journalist Whistleblowing) |
+---------------------------------------------------------------+
| 💬 FORUMS & COMMUNITY (Medium Risk) |
| |
| • Dread (Current Address Required) • DarkForums Onion |
| • The Hidden Wiki (Verify Working Link) |
+---------------------------------------------------------------+
| ⚠️ ADULT & SPECIALIZED (High Risk - Use Caution) |
| |
| • Dark Web Porn Directories • Niche Hobby Forums |
| • Verified Market Access Points (Escrow Only) |
+---------------------------------------------------------------+
Directory Categories & Risk Assessment
Directories in 2026 generally organize links into the following primary categories. A comprehensive safe .onion sites list will categorize these clearly to help you navigate risk.
| Category | Description | Risk Level | Example Use Cases |
|---|---|---|---|
| Communication | Secure email, instant messaging | Low | ProtonMail .onion, SecMail |
| Privacy & Security | Tools, encryption software, VPNs | Low | Tor Project mirrors, Privacy guides |
| Research & Archives | Digital libraries, whistleblowing | Low | Sci-Hub, Global Leaks directories |
| Forums & Communities | Discussion boards, tech support | Medium | Dread (Reddit alternative), Hacker forums |
| Financial Services | Crypto tumblers, exchanges | High | Bitcoin mixers, Monero swapping services |
| Marketplaces | E-commerce (legal & illegal goods) | Very High | Varied (high rate of scams and clones) |
| Adult Content | Indexing sites for adult material | High | Dark web porn directories (Caution advised) |
Why Accessing the Dark Web is Difficult
Wrong Habits
Many users try to open onion links in standard browsers like Chrome or Safari, which are not built to handle onion routing. Standard browsers do not know how to communicate with the Tor network's entry nodes. When you paste an .onion link into Chrome, the browser tries to resolve it using standard DNS servers, which inherently do not recognize the .onion Top Level Domain (TLD).
Outdated Information
Websites on the darknet go offline frequently, meaning lists from even six months ago are often useless. Sites disappear for many reasons: server seizures by law enforcement, voluntary shutdowns by admins, DDoS attacks from rival groups, or simple domain expiration. Furthermore, the Tor Project entirely deprecated V2 .onion addresses (which were 16 characters long) in late 2021. Any directory still listing V2 links is completely obsolete.
Misunderstanding the Tech
Some people believe the dark web is just one place, rather than a decentralized network of individual nodes. The dark web is not a physical location or a single server; it is a layered overlay network running on top of the regular internet. If one node goes down, the rest of the network continues to function independently.
External Limitations
Slow connection speeds are normal because the Tor network bounces your data through three different global servers to ensure privacy. This process—known as onion routing—intentionally adds latency. Your data is encrypted multiple times and sent through a random path of Entry Node, Middle Node, and Exit Node.
5 Common Dark Web Directory Mistakes
1. Clicking Links from Unverified Sources
Users often follow links from social media or public forums that lead to phishing sites designed to steal data. In the current era, phishing on the dark web is highly sophisticated. Scammers create exact pixel-perfect clones of popular directories or marketplaces. When you type your credentials into these fake sites, the scammers capture them and immediately try to access your real accounts or crypto wallets.
Fix: Use a dark web safety guide 2026 to learn how to check the reputation of a directory before clicking. Always look for PGP signatures from the directory's known administrators. If a directory claims to be the "Official Hidden Wiki," verify its PGP key against trusted key servers before interacting with it. Clones are rampant, so skepticism is your best defense.
2. Failing to Use a VPN with Tor
Your internet provider can see that you are using Tor, even if they cannot see what you are doing—this can sometimes flag your account for investigation. While Tor hides what you are doing, it does not hide the fact that you are connecting to the Tor network. In some countries, simply using Tor is viewed with suspicion, and ISPs may throttle your bandwidth or report the usage to authorities.
Fix: Connect to a reputable VPN first then open the Tor Browser to create a double layer of privacy. Your ISP will only see that you connected to a VPN server, not that you subsequently opened Tor.
| VPN Feature Required for Tor | Why It Matters |
|---|---|
| Strict No-Logs Policy | Ensures no record of your Tor usage exists if servers are seized |
| Kill Switch | Prevents your real IP from leaking to your ISP if the VPN drops |
| RAM-Only Servers | Wipes all data upon reboot, leaving no physical trace of your session |
| Obfuscation/Stealth VPN | Hides the fact you are using a VPN from deep packet inspection (DPI) |
3. Keeping the Browser Window Maximized
Websites can use "browser fingerprinting" to determine your screen resolution, which helps identify you among other users. If you maximize the Tor Browser to fit your 4K monitor, your browser fingerprint instantly stands out. The vast majority of Tor users browse with the default, smaller window size. By maximizing it, you make yourself a unique outlier, making it easier for advanced trackers to follow you across different .onion sites.
Fix: Keep the Tor Browser window at its default size to blend in with thousands of other anonymous users. Never resize it.
4. Mixing the Dark Web with the Deep Web
Many people confuse private databases with the darknet, leading to safety errors. The deep web includes your online banking portal, your private email inbox, and password-protected university library databases. These require standard logins but are not part of the Tor network. The dark web is a specific subsection of the deep web that requires specific software (like Tor) to access.
Fix: Read our breakdown on the dark web vs deep web vs clearnet to understand exactly where you are browsing.
| Attribute | Deep Web | Dark Web |
|---|---|---|
| Requires Special Software? | No (Standard browser) | Yes (Tor, I2P, Freenet) |
| Content Type | Private databases, medical records, bank accounts | Anonymous forums, unregulated markets, whistleblowing sites |
| Security Risk | Standard clearnet risks (phishing, hacking) | High risks (malware, scams, illegal content exposure) |
5. Trusting Every Market Listing
New users often assume all listed services are functional but many are "exit scams" or fake clones. An exit scam occurs when a marketplace or vendor builds up a good reputation, collects funds from users, and then suddenly disappears with the money. In 2026, automated bots frequently scrape legitimate market directories and create fake clone sites to steal deposits.
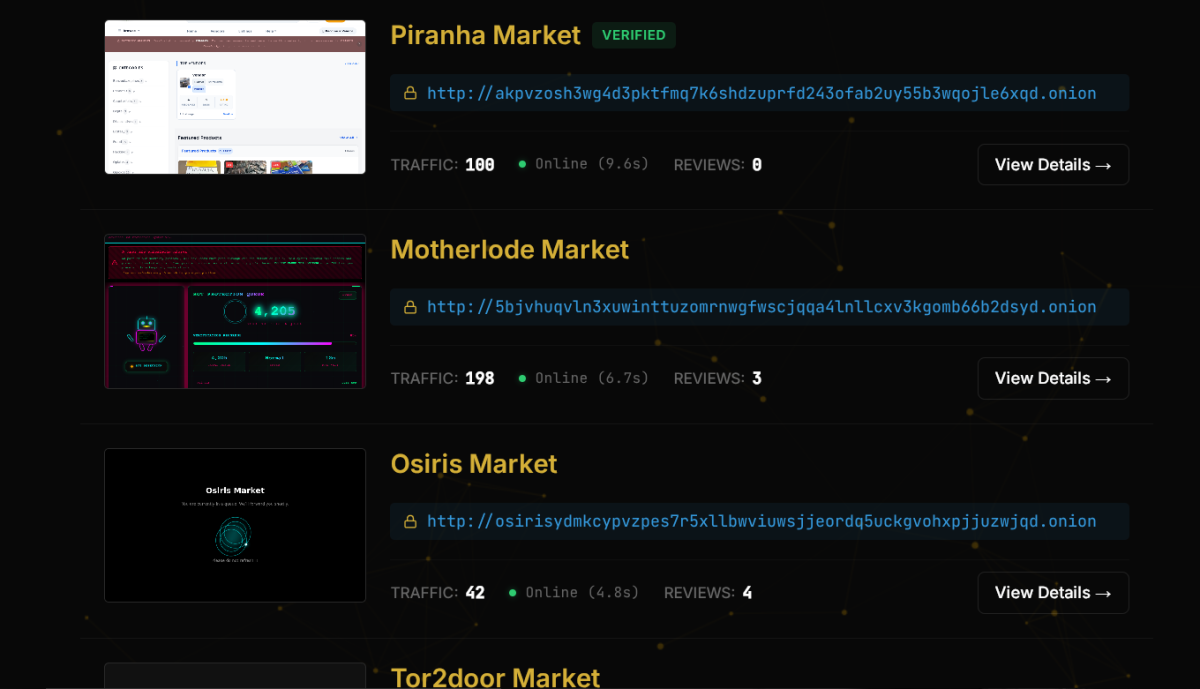
Fix: Check current status reports on verified platforms like Piranha Market to confirm they are online. Additionally, read our analysis on active darknet markets 2026 to understand what's real, what's fake, and what to avoid. Only trust marketplaces that have a long history of consistent uptime and verified community feedback, and always cross-reference with a list of verified dark web marketplace onion URLs.
How to Access Verified Onion Sites (Step-by-Step)
Step 1 - Secure Your Hardware and Connection
Download the official Tor Browser 15.0.13 (updated with Tor 0.4.9.8) from the Tor Project website. Do not get it from third-party sites. Third-party sites often host modified versions of the browser that contain built-in malware or tracking scripts. Connect your VPN to a server in a privacy-friendly country to mask your initial connection point.
For a detailed walkthrough of this process, refer to our complete access onion sites 2026 safe Tor setup guide.
Advanced Hardware Security: For maximum safety in 2026, consider using a dedicated operating system. Instead of running Tor on your daily-use Windows or macOS machine (which can suffer from memory leaks or background apps exposing your IP), boot into a privacy-focused OS like Tails (The Amnesic Incognito Live System) or Whonix. Tails runs entirely from a USB stick and leaves no trace on your computer once you shut it down.
Step 2 - Locate a Verified 2026 Directory
Find a reliable entry point. You can use the "99% of the internet explained" guide to find reputable starting links. Copy the onion address and paste it directly into the Tor URL bar.
How to verify a link:
- Check if the directory is listed on multiple, unconnected community forums.
- Look for a valid PGP signature on the directory's homepage.
- Use dark web search engines (like Ahmia or Torch) to search for the directory's name and see what the community is saying about it.
Step 3 - Navigate by Category
Use the internal search tools within the directory to find what you need. Avoid downloading any files unless you are in a "sandbox" environment, as files can contain tracking scripts. If you are looking for specific tools or communities, knowing the exact name helps—searching for "Cebulka" or "Cracking Island" requires precise queries in these search bars.
Common Problems & Fixes
Problem - The Onion Link Says "Unable to connect"
Fix: Check your system clock - If your computer time is wrong, Tor cannot sync with the network. If the time is correct, the site is likely down or moved.
Why does the clock matter? The Tor network relies on precise cryptographic consensus. If your computer's clock is off by even a few minutes, the SSL/TLS certificates used by the Entry and Exit nodes will appear invalid to your browser. The Tor Browser will refuse to connect to prevent potential man-in-the-middle attacks. Always ensure your operating system is set to sync time automatically.
Problem - The Page is Loading Too Slowly
Fix: Click the "New Circuit for this Site" option in the Tor menu - this moves your connection to a faster set of relays.
Understanding Tor Circuits: Every time you visit a new .onion site, Tor builds a "circuit" (Entry Node -> Middle Node -> Exit Node). If the nodes chosen for your current circuit are overloaded or geographically distant from you, the site will load incredibly slowly. By selecting "New Circuit for this Site," you force Tor to drop the current connection and randomly select three new, hopefully less congested, nodes.
Problem - I Am Worried My Info Is Already Leaked
Fix: Use dark web monitoring tools to scan for your email or passwords in known data breaches. If you have used the same password on the clearnet that you accidentally typed on a dark web phishing site, you must assume it is compromised.
| Monitoring Tool Type | What It Does | Recommended Action |
|---|---|---|
| Breach Scanners | Searches known databases for your email/phone | Change passwords immediately if found |
| Dark Web Scanners | Continuously monitors Tor for your specific data | Use services like Have I Been Pwned or premium identity protection |
| Credit Monitors | Alerts you to new accounts opened in your name | Freeze your credit if you suspect deep identity theft |
Safety & Best Practices
- Never use your real name, email or photo on any onion site. Create a completely separate digital identity if you plan to participate in forums. Use a pseudonym that you have never used on the clearnet.
- Disable JavaScript in the Tor Security Level settings (set it to "Safest") to prevent malicious scripts from running. JavaScript is the number one vulnerability on the dark web. It can be used to force your browser to reveal your real IP address or execute malware without your knowledge.
- Cover your webcam with physical tape while browsing as an extra precaution. While browser exploits are rare if you keep JavaScript disabled, physical surveillance via malware (like Remote Access Trojans) is a threat if you accidentally download an infected file.
- Avoid checking your personal bank accounts or social media while the Tor session is active. If you log into your real Facebook or bank account through the Tor browser, you are linking your anonymous Tor activity to your real-world identity, completely defeating the purpose of using the browser.
- Never buy illegal items. This guide is provided for educational, privacy, and research purposes. Engaging in illegal activities not only puts you at risk of prosecution but also funds dangerous criminal enterprises. For those interested in the market aspect strictly for research or legal goods, we have compiled a list of the top 3 active tor markets 2026.
FAQ
Q: Is browsing a Dark Web Directory illegal? A: In most jurisdictions, browsing a directory is legal, provided you do not access illegal content or purchase illicit goods. While using Tor is legal, clicking on links that host illegal material (such as abusive content) can violate local laws. Always stick to verified, safe directories to minimize legal risk.
Q: Can I access onion links on my phone? A: Yes, you can use the official Tor Browser for Android or Onion Browser for iOS. Always ensure you are using the official apps to avoid malware.
| Device / OS | Recommended App | Security Limitations |
|---|---|---|
| Android | Tor Browser (Official by Tor Project) | Some custom Android ROMs may have background tracking |
| iOS (iPhone/iPad) | Onion Browser | iOS sandboxing is strong, but Apple restricts some network APIs, making Tor slightly less configurable than on Android |
| Desktop (Windows/Mac) | Tor Browser | Higher risk of background apps leaking data compared to a Live USB |
| Desktop (Tails Linux) | Built-in Tor System | Most secure option; routes all system traffic through Tor, amnesic |
Q: Why do onion links look like random gibberish? A: These addresses are cryptographic hashes of the site's public key. This design prevents forgery and ensures anonymity by verifying you are connecting to the server holding the correct private key, rather than relying on a central domain registrar.
Q: How do I know if a directory link is a scam? A: Verify the link against multiple independent sources and look for a valid PGP signature. Avoid directories with excessive ads, broken English, or those asking for login credentials to view links. A legitimate directory functions as a library catalog—it shouldn't need your personal data just to show you the list of sites.
Red Flags of a Scam Directory:
- No PGP Signature.
- Too many pop-up ads for sketchy VPNs or crypto.
- Poorly translated text with heavy grammatical errors.
- Asks you to log in just to view links.
Q: How do I find the current Dread forum address? A: Check verified clearnet news sites that cover darknet security or trusted link aggregator mirrors. Never trust random Pastebin links claiming to be the URL. Always verify the working link on multiple sources before entering your credentials.
Q: Are there mainstream sites on the Dark Web? A: Yes, major organizations like Facebook, the New York Times, and the CIA maintain official onion addresses. Aside from the current Facebook onion address, you can find the official Tor Project onion address and various news outlets. The Internet Archive onion address is also a popular safe destination. These are considered safe examples and good places to test your browser configuration.
Q: What is the difference between Tordex and standard directories? A: Tordex functions as an automated search engine crawler for .onion sites, whereas standard directories are usually human-curated lists. While Tordex can help find obscure content, it carries a higher risk of indexing phishing sites compared to human-curated lists.
Q: What about specialized tools like OnionGPT? A: Tools like OnionGPT represent experimental, uncensored AI services available on the network. These are often experimental and lack the safety rails of commercial AI. Users should approach them with the same caution as any other executable or script on the dark web.
Final Verdict
Finding a reliable Dark Web Directory in 2026 requires patience and the right tools. Many users fail because they use old links or forget basic security steps like hiding their IP address. The landscape of the hidden web is not static; it is a highly volatile environment where links die, directories change hands, and threats evolve constantly. Relying on outdated information from years past is the quickest way to compromise your digital security or fall victim to a phishing scam.
Whether you are hunting for the current working Dread link, looking for the Rutracker onion link, or simply trying to access the Facebook onion address, the core principles remain the same. By following this guide and using verified links, you can explore the hidden web safely. Remember that anonymity, skepticism, and compartmentalization are your best defenses. Always use a VPN, keep your browser window at the default size, set your security level to "Safest," and never bridge your real-world identity with your dark web browsing session. Stay curious, but always prioritize your digital security.